This Is Not Protest vs Police — It’s Civilians Trapped in the Middle
The situation unfolding between federal immigration enforcement and digital opposition groups is often framed as protest versus policing or vice versa. That framing misses what is actually happening.
This is a surveillance‑infused standoff—a form of low‑intensity digital warfare where the state deploys advanced surveillance systems, while hostile non‑state actors respond with cyber exposure, intimidation, and calls for harm. The public is not watching from the sidelines. Civilians are the terrain.
No side emerges clean from this.
One Front of the War: State‑Level AI Surveillance Goes Citywide
Federal immigration enforcement has become a proving ground for modern surveillance operations. Using large budgets, agencies have expanded beyond traditional investigative methods into continuous digital monitoring.
This includes:
AI‑powered facial recognition deployed in public spaces
License‑plate readers creating persistent movement histories
Social‑media scraping and sentiment analysis
Location and metadata acquisition via data brokers
Simulated cell‑tower technology that captures nearby phone identifiers
These systems do not distinguish cleanly between targets and bystanders. Anyone within a digital radius—physically or online—can be swept into collection simply by proximity.
From a systems perspective, this is birds‑eye surveillance: high‑resolution visibility across cities, events, and communities. Once collected, data is retained, correlated, and re‑queried.
The impact is broader than immigration enforcement. It reshapes public life.
The Other Front: When Activism Turns Into Weaponized Hacktivism
Opposition has not remained purely civic or defensive.
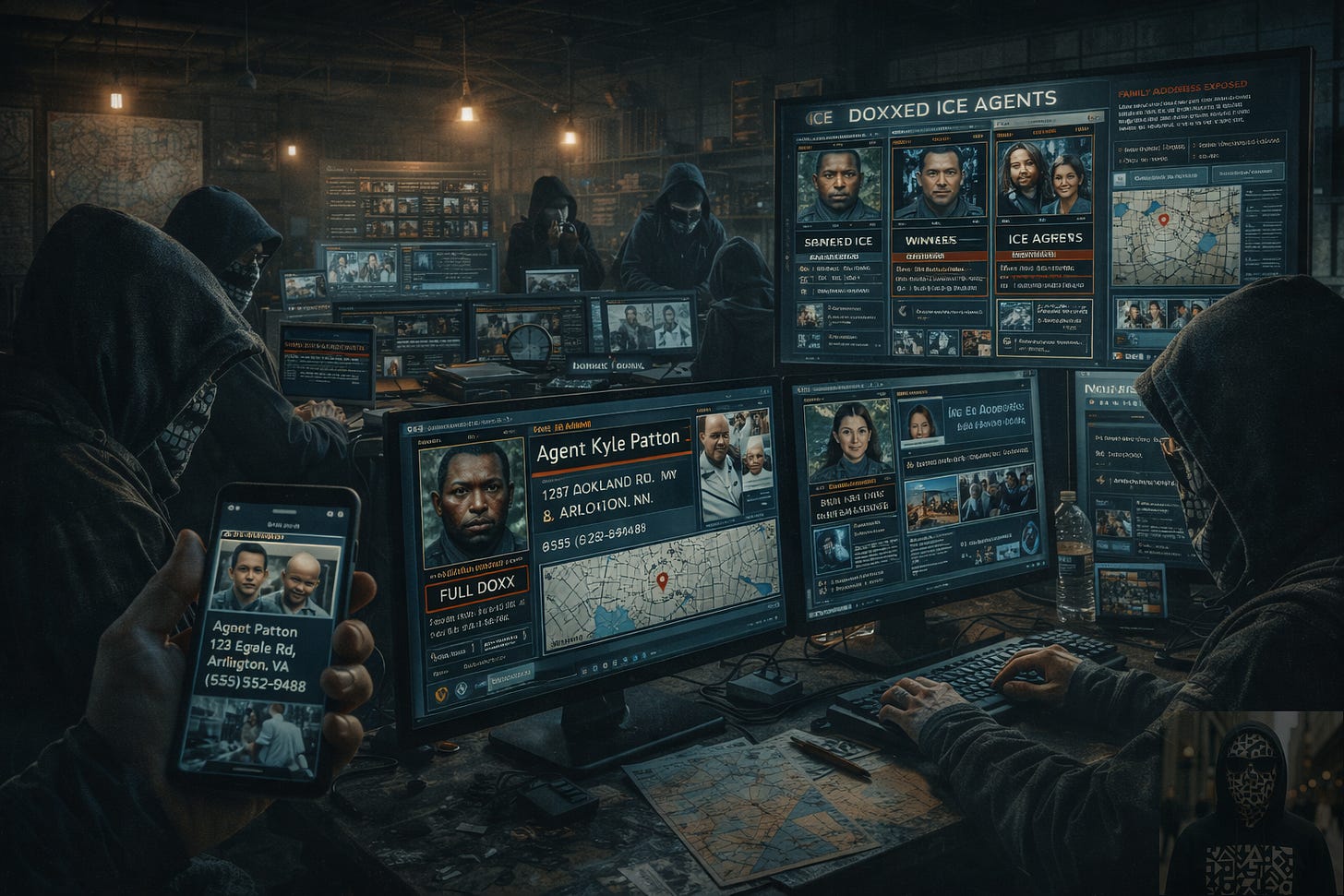
What began as documentation and accountability has, in some circles, escalated into hostile hacktivism—using digital tools not only to observe the state, but to expose, intimidate, and threaten individuals.
Documented tactics include:
Publishing names, photos, and social‑media profiles of agents
Exposing home addresses and family connections
Mapping surveillance infrastructure and operational movements
Coordinating mass online harassment campaigns
Encrypted channels used to share real‑time enforcement locations
In the most extreme cases, rhetoric has crossed into explicit calls for violence, including threats toward agents’ families and encouragement of physical harm.
At this point, these actors are no longer functioning as activists. They are operating as non‑state digital combatants.
This matters because it changes incentives on all sides.
Escalation Is the Strategy — And No One Is De‑Escalating
This is the core dynamic most people fail to see.
What’s happening is not a temporary spike in tension or a communication breakdown. Escalation itself has become the operating logic on both sides of this standoff.
For federal agencies, escalation is framed as a necessity:
More surveillance is justified as protection against leaks, threats, and exposure
Broader data collection is defended as risk management
Automation is adopted to keep up with the scale of perceived hostility
Every act of doxxing or threat is used to argue that less visibility is dangerous—therefore, more surveillance is required.
For hacktivist groups, escalation is also framed as a necessity:
Expanded surveillance is cited as proof that exposure must intensify
Publishing identities and locations is justified as deterrence or accountability
Rhetoric hardens as retaliation and attention increase
Every new surveillance tool becomes evidence that soft tactics no longer work—therefore, more aggressive exposure is required.
This creates a closed loop:
Surveillance justifies exposure
Exposure justifies surveillance
Each cycle increases speed, scope, and automation
Crucially, neither side is incentivized to slow down.
Backing off looks like weakness. Restraint looks like vulnerability. Transparency is treated as a liability.
There is no trusted referee. No shared rules. There is no clear boundary separating targets from bystanders.
In this environment, escalation isn’t a failure of strategy.
It is the strategy.
Civilians Are the Collateral Damage
This is the part that almost no one explains clearly.
Most people caught in this standoff are not activists, agents, or targets. They are ordinary people using a phone, a laptop, or a car—without realizing how much signal they are emitting.
In a surveillance‑infused environment, simply existing digitally creates exposure.
1. Your phone is a tracking device—whether you consent or not
When you carry a smartphone, you broadcast identifiers constantly:
Cell‑tower pings that reveal location and movement patterns
Wi‑Fi and Bluetooth signals that nearby systems can log
App metadata showing who you talk to, when, and how often
Simulated cell‑tower systems and bulk metadata collection do not need your content. Location, timing, and association are enough to map your life.
If you are near a protest, enforcement action, or sensitive area—even briefly—you can be collected as a bystander.
2. Your computer and tablet leak behavior, not just data
Every browser tab, login, and scroll produces behavioral signals:
IP address and rough location
Device fingerprinting (screen size, OS, browser configuration)
Account associations across platforms
You do not need to post anything political to be profiled. Patterns alone can place you inside datasets built for surveillance or counter‑surveillance.
3. Hacktivist exposure doesn’t stay “targeted.”
When hostile groups publish identities, maps, and operational details, the blast radius expands:
Neighbors, relatives, and unrelated people get swept into exposure
Addresses and locations become permanent online artifacts
Misinformation and mistaken identity travel faster than corrections
This is how civilians become collateral—not through intent, but through proximity.
4. Once collected, data rarely disappear
Data captured today can resurface years later—re‑analyzed under new rules, new models, or new political climates. There is no meaningful expiration date.
This Is What Modern Warfare Looks Like Now
Not kinetic. Not declared.
A form of urban digital conflict where:
The state seeks total visibility to maintain control
Non‑state actors seek exposure and disruption
Automation replaces human judgment
Civilians absorb the consequences
This model does not stay localized. It spreads city by city.
How to Protect Yourself While This Escalates
There is no way to opt out completely—but there are professional‑grade steps that materially reduce exposure. This is about risk reduction, not paranoia.
Digital protection (what actually works)
Use a reputable VPN to mask IP‑based location and reduce passive tracking across networks
Prefer end‑to‑end encrypted messaging for sensitive conversations (where the provider cannot read content)
Lock down app permissions—especially location, Bluetooth, microphone, and background access
Use privacy‑focused browsers with tracker blocking by default
Avoid linking real identity across multiple platforms unnecessarily
Encryption does not make you invisible—but it narrows what can be collected.
Device discipline
Keep operating systems and apps updated (many exploits target old versions)
Do not install unknown apps or browser extensions
Separate personal, work, and sensitive accounts when possible
Physical‑world awareness
Assume public spaces may be monitored from above and at street level
Avoid carrying multiple always‑on devices to sensitive locations
Do not livestream or post real‑time location during tense events
Remember: proximity alone can place you in datasets
These steps reduce the data surface area available to both state surveillance and hostile non‑state actors.
Why This Exists (And Why Awareness Is the Only Shield)
This is not about taking sides.
It is about understanding the environment we are entering.
A world where surveillance is normalized, exposure is weaponized, and ordinary people are caught between state systems and hostile networks.
Awareness is the first form of protection. Join the Movement
AI doesn’t need to be evil.
It only needs to be wrong.
What you’re reading isn’t theory — it’s a record of what’s already happening.
This space exists to make it visible before it becomes normal, and to connect people who refuse to accept permanent surveillance as the cost of living.
If you’re here, you’re already part of it.
Join the movement.
Subscribe to stay inside the signal and get access to verified cases, source documents, NotebookLM research, videos, and practical ways to reduce exposure.
Quiet. Grounded. Real.
→ Join the movement